Guide
How Strong is Your MDM Security?
When you're managing fleets of dedicated devices, your MDM security isn't just about device management. It's about protecting your business, your customers, and let’s be honest, your career.
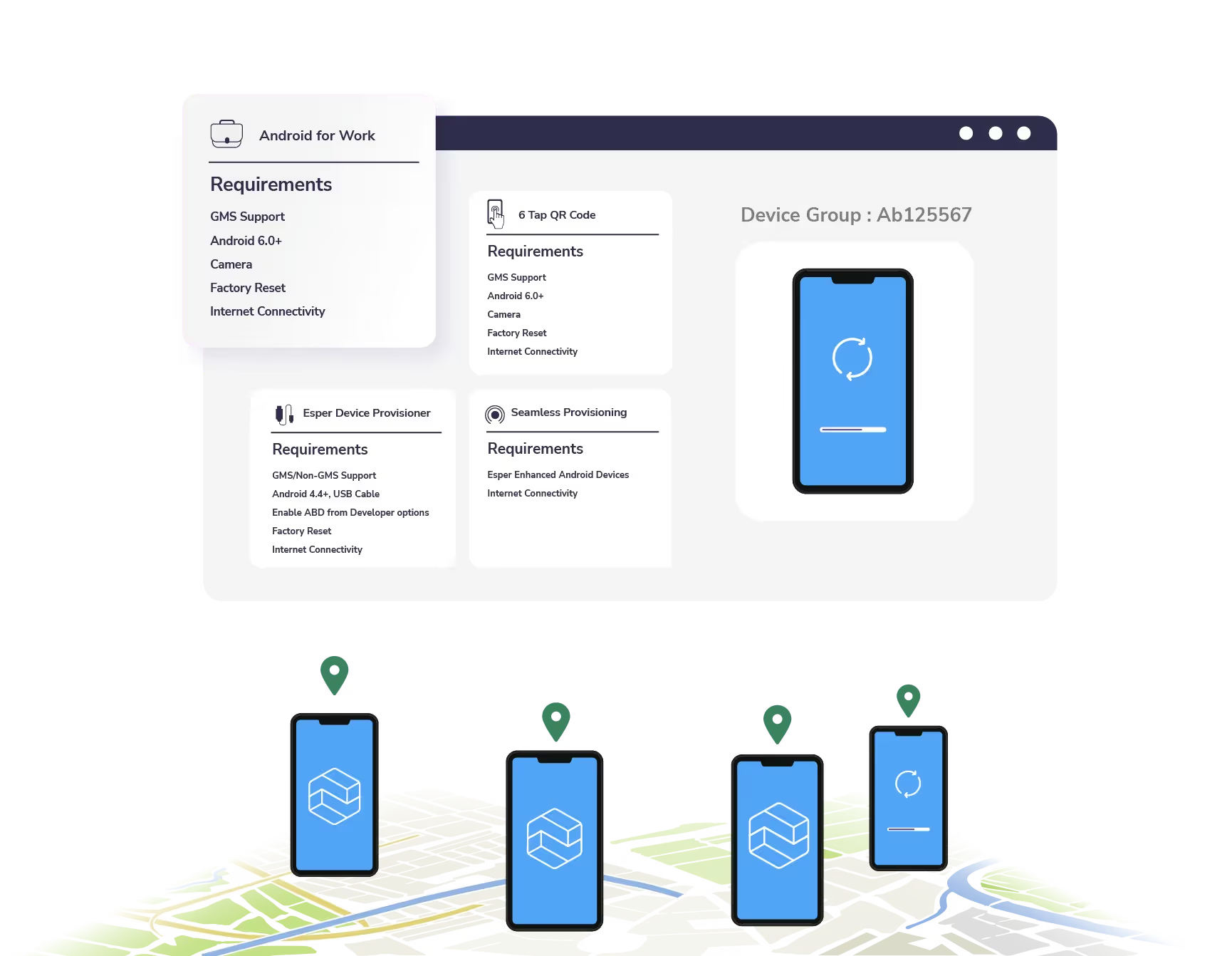
The challenge? Most MDM solutions were built for smartphones and bring-your-own-device (BYOD) scenarios, not the specialized security needs of dedicated enterprise devices. This guide highlights six key layers and 36 security touchpoints for a self-executed deep security analysis of potential risks within your MDM.

You Can’t Afford To Ignore Strong MDM Security
The average cybersecurity breach costs $4.35 million. Don’t let your MDM be the weak link in your organization’s digital security chain.
You can self-audit your MDM’s security practices today to ensure maximum protection for your customers, devices, and company. With this guide, you’ll learn the high-level questions you need to ask to assess your MDM’s security posture, how to analyze each of the six MDM security layers, and steps you can take to maximize security practices on your dedicated devices.
Don’t wait for a security breach to affect your company and customers — download this guide and checklist before it’s too late.
quick tip
Did you know? Your MDM’s security practices start at the cloud level and extend all the way to the user experience. The devices, app experience, and network practices all play a critical role in proper MDM security.
GET YOUR COPY



