There are several valid reasons to downgrade or rollback an update to an Android app, but the OS doesn’t provide a way to do so without using developer tools. Downgrading an app can cause problems if the app’s data isn’t cleared, but bugs and stability issues aren’t the only problems to consider. Rolling back an update can expose the device to security vulnerabilities that exist in older versions of the software. That’s why Android now no longer lets users downgrade system apps beyond the factory installed version.
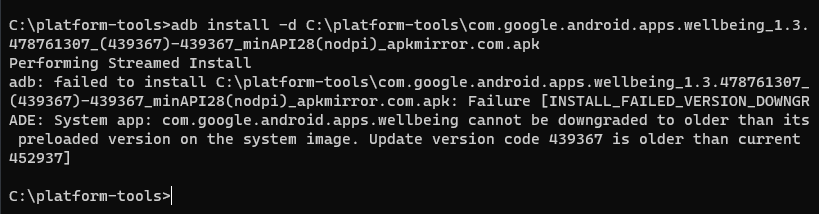
Devices that have applied the latest Android security patches detailed in the May 2023 Android Security Bulletin are now protected against CVE-2023-21116, an escalation-of-privilege (EoP) vulnerability that made it possible to roll back a system app below the system image version. A patch is available for AOSP versions 11-13 that fixes a logic error in the verifyReplacingVersionCode method of the InstallPackageHelper class. For testing purposes, Android still allows downgrading a system app beyond the factory version if the build or app is marked debuggable, but otherwise, the INSTALL_FAILED_VERSION_DOWNGRADE error will be given.
Since this vulnerability can only be readily exploited by an attacker with ADB or shell privileges, it makes sense why it only has a severity rating of “moderate.” Ordinary, user-installed apps or attackers without physical access to the device can’t pass the necessary flag to initiate an app downgrade, so the existence of this vulnerability should not concern most users and admins who have yet to or cannot update their devices to the May 2023 security patch level (2023-05-0X). Still, it is worth applying the update as soon as it is made available, as older versions of system apps may have vulnerabilities that can be chained into escalating privileges or exfiltrating sensitive data.
For example, a vulnerability in older versions of the Samsung TTS app can be exploited to escalate the privileges of a regular app to the system level. This vulnerability, assigned CVE-2019-16253, was identified and fixed in 2019 but could still be exploited by downgrading the app to a vulnerable version. Samsung devices with the May 2023 SPL should be fully protected against this vulnerability, as the version of the Samsung TTS app that’s preinstalled in the system image isn’t vulnerable to CVE-2019-16253 and Android won’t allow users to downgrade to a version that is vulnerable.